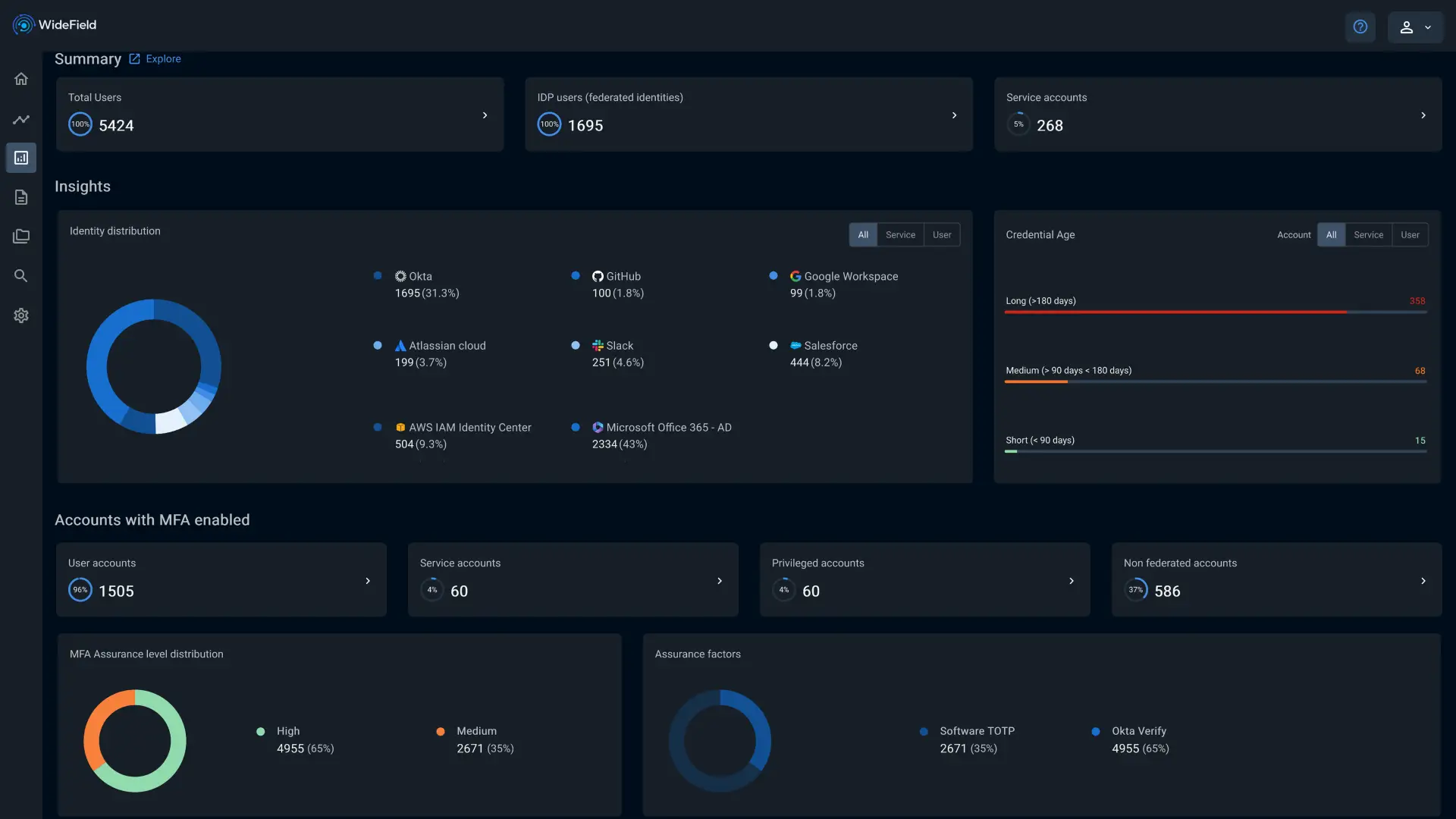
Modernize Your Identity Security for the AI Era.
Just like data, identity must be protected at Rest, in Motion, and in Use. WideField connects your identity fabric across SaaS, Cloud, and on-premises to gain full visibility and detect threats from AI agents, human identities, and non-human identitites (NHIs).
// What's Broken in Identity//
The root causes of identity breaches are hiding in plain sight
Despite massive investment in identity tooling, attackers continue to exploit basic, unresolved flaws. Here's where it breaks down—and how WideField addresses it:
Incomplete Account Lifecycle
Dormant and partially offboarded identities create silent vulnerabilities. Unused accounts become easy targets for lateral movement and privilege escalation.
Weak or Stale Credentials
Stale passwords, unrotated secrets, and shared credentials go unnoticed—leaving wide-open entry points for attackers to exploit.
Posture Drift and Policy Escapes
MFA and access policies are often assumed to be “set and forget.” But over time, changes, exceptions, and misconfigurations lead to policy drift and new risk pathways.
Blind Spots in Token and Session Activity
OAuth tokens and service account sessions often run unchecked. Without behavioral monitoring, attackers can hijack these without detection.
// Our Vision//
The Identity Security Lifecycle
We envisioned a complete identity fabric where identity like data is protected at every phase: at rest, in motion, and in use. Here's how.

Start with visibility
You can’t secure what you don’t know exists. WideField helps you:
- Discover all identities human and non-human
- Map exposures across accounts, roles, and credentials
- Assess hygiene and lifecycle gaps


Secure the front door. Harden your authentication
Strong credentials and MFA aren’t enough. WideField identifies weak authentication paths and policy escapes before attackers can exploit them.
- Detect misconfigurations in authentication policies
- Spot authentication journeys with weak guardrails
- Analyze login telemetry across cloud and SaaS


Watch what identity does, not just how it logs in.
Authentication is not the finish line—it’s just the start. WideField delivers:
- Live session monitoring for real-time threat detection
- AI-powered behavioral analytics
- Coverage across human and machine identities

// How WideField Works//
One platform. Six powerful outcomes.
WideField delivers full-spectrum identity threat protection—from visibility to detection to response. Here’s how it works:
Connect your environment
Collect signals via API from your IAM, SaaS, and Cloud systems. Get started quickly—no agents, no friction.

Discover and assess identity risks
Analyze risks in dormant accounts, overprivileged roles, stale credentials, and more. Surface hygiene issues before attackers find them.
AI powered authentication event analysis
Detect risky login flows and misconfigurations in real time using machine learning and AI. Don’t let one forgotten group break your access policy.
Remediate with speed and precision
Take action manually, via policies, or automate response through APIs. Neutralize threats without user disruption.

AI powered post-authentication session analysis
Track behavior within sessions to catch identity misuse as it happens using AI. Spot anomalies in both human and non-human activity.
Investigate identity behavior across users and machines
Give your SOC a unified view of account activity. Human or bot—track intent, trace patterns, and close the loop.
// Customer Testimonials//
Trusted by Security leaders
WideField is helping security teams modernise identity protection across SaaS and cloud environments. Here’s what our customers are saying
// Get in touch//
Get started in minutes. Address identity risk in hours.
Deploy WideField in minutes and get a complete identity risk assessment in a single day. Connect your stack, analyse threats, and start reducing risk—fast.